前言
这是一个用于”Epic Turla”网络间谍攻击行动中的一个漏洞,PDF的漏洞
漏洞分析
环境
win7 sp1 32位
windbg
ida
peepdf
adobe reader 11.0.00
ftp://ftp.adobe.com/pub/adobe/reader/win/11.x/11.0.00/zh_CN/AdbeRdr11000_zh_CN.exe
安装peepdf
1 | pip install peepdf |
-i开启交互模式
1 | peepdf -i ./msf.pdf |
结果并不是很好使
我们直接复制下面 Q=开始的东西到一个文件里面
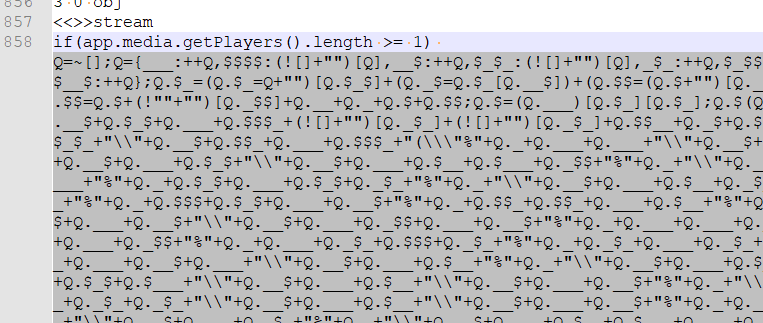
之后即可解密
1 | PPDF> js_jjdecode file jjencode.txt |
那我们分析js,基本也能分析出个东西,除了对喷射,主要的代码就几条
1 | app.addToolButton({ |
调试
我们调试看看,打开的时候最好把保护模式关掉(第一次开启的时候应该会问你),不然我也不知道行不行
1 | (95c.eb0): Access violation - code c0000005 (first chance) |
我们看看前面调用的是什么,可以看劫持控制流的eax来源于esi
1 | 0:000> ub 6219e85d |
我们看看esi,这里由于堆喷已经占位了,所以是busy,这里也可以看到大小是0x370
1 | 0:000> !heap -p -a esi |
懒得找纯正的poc了,不然更能精准看到是uaf


