分析ActionScript虚拟机源码辅助漏洞调试
原书ActionScript写错了
环境
win7 sp1 32位
windbg
ida
flash player下载地址
http://download.macromedia.com/pub/flashplayer/installers/archive/fp_16.0.0.296_archive.zip
(建议使用vps下载,国内有可能被劫持)
历史版本页面
https://helpx.adobe.com/cn/flash-player/kb/archived-flash-player-versions.html
下载后安装的是flashplayer16_0r0_296_winax.msi,后来用exe还是不行【我分析个漏洞容易吗】,那我按照不带ax的flashplayer16_0r0_296_win.exe
不用ax的安装包也能崩溃,不过esi看不出是什么来
1 | (d18.908): Access violation - code c0000005 (first chance) |
我们还是跟着作者的思路分析去
用
1 | public class Main extends Sprite |
worker进程
1 | private function workerThread() : void |
onMessage
1 | private function onMessage(param1:Event) : void |
接下来简单看看AVM的源码:https://github.com/adobe-flash/avmplus
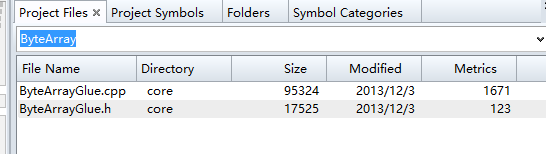
Source Insight 打开后,搜索ByteArray
我们看看cpp,在左边函数窗口搜索clear即可定位到clear函数
1 | void ByteArray::Clear() |
这里调用的task.run,我们继续跟踪
1 | class ByteArrayClearTask: public ByteArrayTask |
我们在函数列表搜一下
1 | void ByteArray::UnprotectedClear() |
其实后面作者就是通过查找到函数在ocx文件中的偏移,下对应的条件断点,可观察到从存在到被清空,到重引用的数据


