实验环境
windows 7
ida
JPEXS Free Flash Decompiler
Adobe Flash Player 10.3.181.22
样本分析
软件下载:http://fpdownload.macromedia.com/get/flashplayer/installers/archive/fp_10.3.181.22_archive.zip
国内下载建议翻墙,国内被2144.com代理了
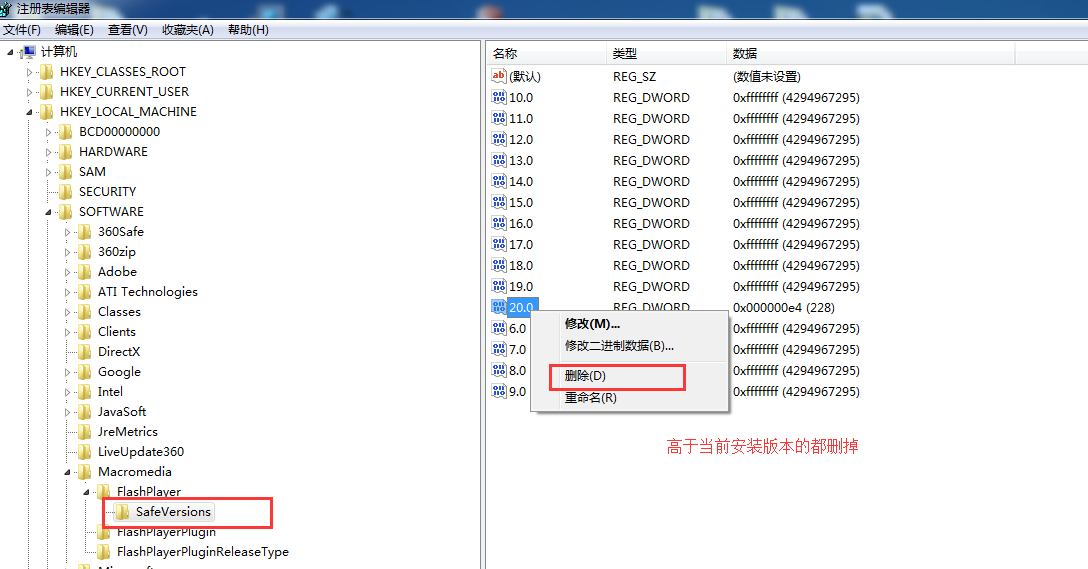
安装限制解决
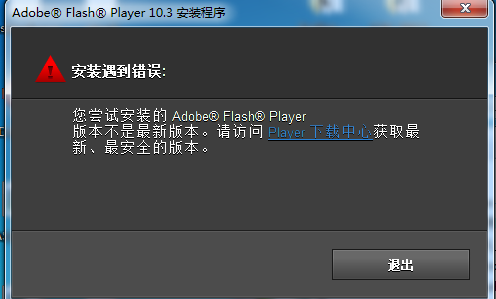
修改注册表就好,(假如安装10.3.xxx,10也要删掉)
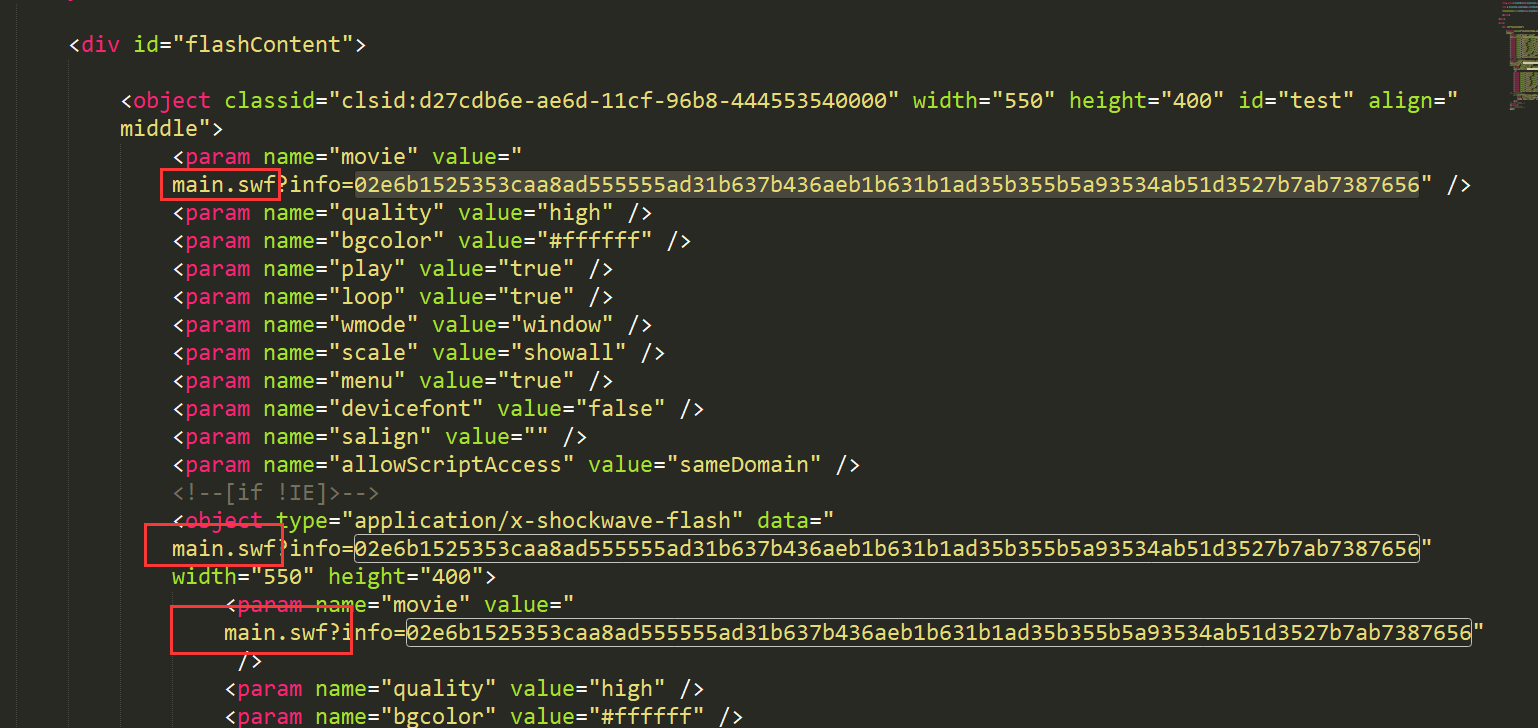
打开样本,可以看到,样本是加载main.swf,并传递一个info的参数
是根据是否为IE浏览器而设置的,第一处是针对IE,第二三处是针对非IE的(有个叹号嘛)
我们反编译下swf,并搜索info,查看对info参数的操作
这是将info参数转化为二进制后,再每个字节异或122,最后uncompress
1 | var param:Object = root.loaderInfo.parameters; |
作者用perl,我们用python
1 | import binascii |
解码结果是这个,当然现在肯定访问不了,用作者的
1 | http://www.amcia.info/down/cd.txt |
这个文件是加密了的
1 | if(!(browser.toLowerCase().indexOf("msie") > 0 || browser.toLowerCase().indexOf("firefox") > 0)) |
给URLLoader的COMPLETE事件加了个onLoadComplete
1 | onLoadComplete = function(param1:Event):void |
python解密
1 | import zlib |
结果是一个加了壳的PE程序
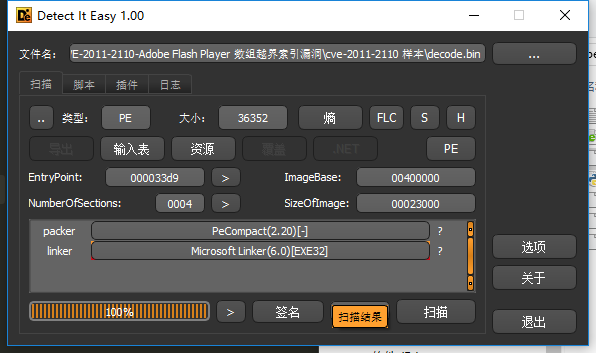
金山火眼好像下架了,看看腾讯哈勃
https://habo.qq.com/file/showdetail?pk=AD0GZ11tB2YIMVs5
virustotal的
行为挺多的,virustotal的也可以看到是游戏相关的木马
后面的看了下,比较懒。。。。。。,先不搞了
本地搭建服务器复现漏洞不错
将exp改为poc调试也是不错的操作
还有就是查看修补补丁的时候,没有match到函数,可以搜索漏洞的指令对应的16进制


